After reading our previous blog post, you might understand what cryptocurrencies are and what blockchain technology is. However, you might also want to know about the basics of how they actually work without being controlled by one central authority or server. Blockchain technology is based on more than just computer code. For the most part, it is heavily related to mathematics. In “The Blockchain: A Gentle Four Page Introduction”, Jan Witte explains that blockchain technology is built upon two mathematical concepts: hash tables and a term within Cryptography (hence, the “crypto” in “cryptocurrency”) known as public key encryption.
Hash tables and hash functions are terms primarily used in the field of computer science. One aspect of this field is the exploration of techniques used to create lists that store data—such as employee records, for example—on a computer. A hash table is one such technique, and it generally works like this: An item in a list, such as an employee record, is given a unique value called a key. Ideally, this key is a number, or a string of characters that can be converted to a number. When this key and the size of the list become the input values of a mathematical function called a hash function, the result is the index, the number representing the place in the list (1st, 2nd, 3rd, etc.). The hash function is typically just an application of the modulus operator; that is, it gets the remainder of dividing the key number by the total number of items that could be contained in the list. If a new item must be added to a list, but the list is very large (think about thousands of employee, product, or transaction records), doing a little bit of math is faster for a computer than searching through an entire list, slot by slot, until an empty slot is found.
Public key encryption also involves mathematics, except the “keys” are functions. It basically works like this: Every party has both a private key and a public key. In order for one party to send a message to another, they must encrypt their message using the other party’s public key. The other party could decrypt the message encoded with their public key by using their private key. Essentially, the “public” and “private” functions are inverses of one-another, so that if the message is the input of one function, and the result of that calculation is the input of another function, the result of that calculation is … The original message. Rivest–Shamir–Adleman (RSA) encryption is a notable example of public key encryption, and like hash tables, the modulus operator is involved in calculations.
Both encryption and hash keys form the basis of cryptocurrency “mining,” or “cryptomining.” Although the power used by cryptomining can surpass the power used by mineral mining according to Max Krause and Thabet Tolaymat, whose Nature Sustainability article was published in 2018, cryptomining has nothing to do with “real” mining. According to Witte, when a cryptocurrency transaction is initiated, it must be stored in the blockchain by using a new hash key that encodes both the new transaction data and the previous hash key. The process of generating the new hash key requires a special cryptographic number called a “nonce,” and different cryptomining computers compete to be the first to find one. The owner of the winning computer receives units of the cryptocurrency in exchange for assistance in completing the new transaction.
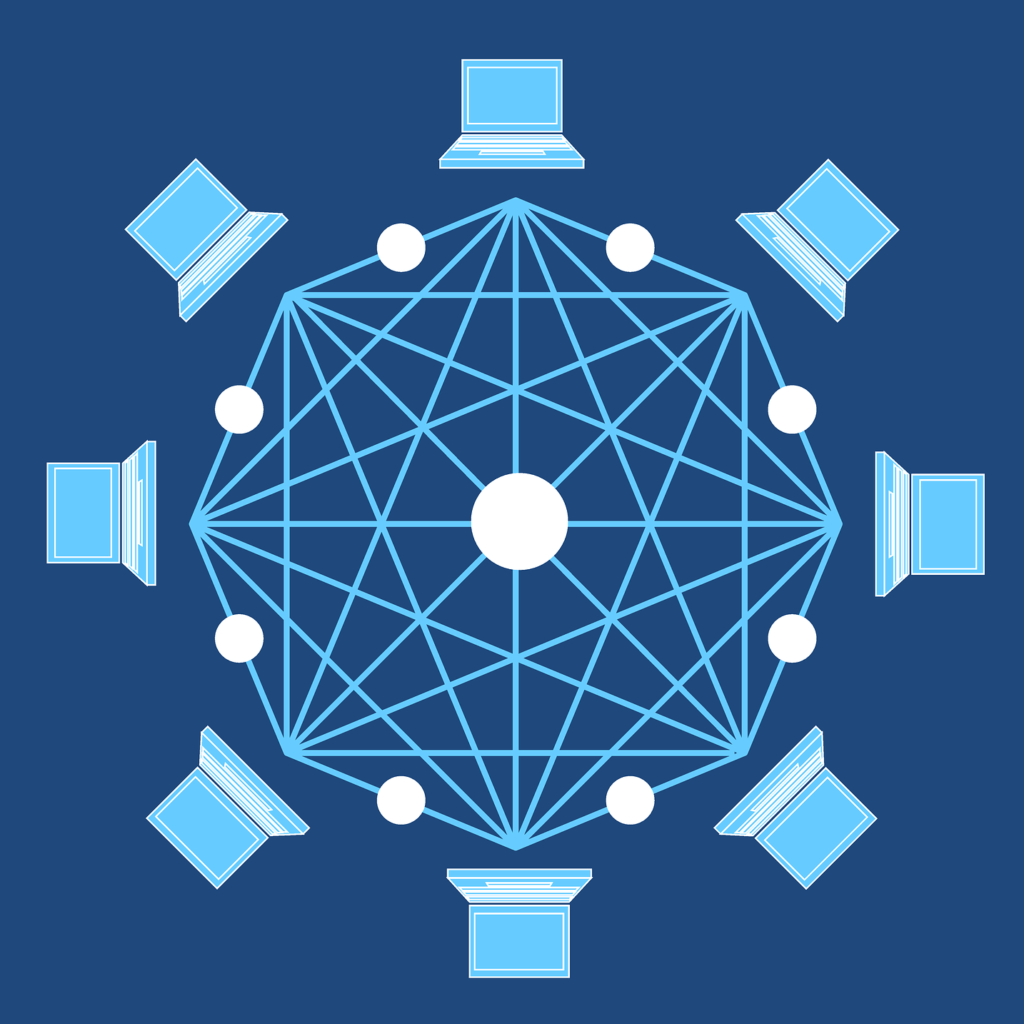
By competing to process new transactions, every cryptocurrency “miner” is also a bookkeeper who maintains the financial aspects of the system. By using previous hash keys to make new ones, cryptocurrency transactions are linked together in an overall “chain.” The process behind adding “blocks” to a “blockchain” isn’t magical—it’s mathematical, and it isn’t beyond the understanding of those who are primarily interested in the business applications of blockchain technology.

1 Comment. Leave new
A great article! Thank you Evan!