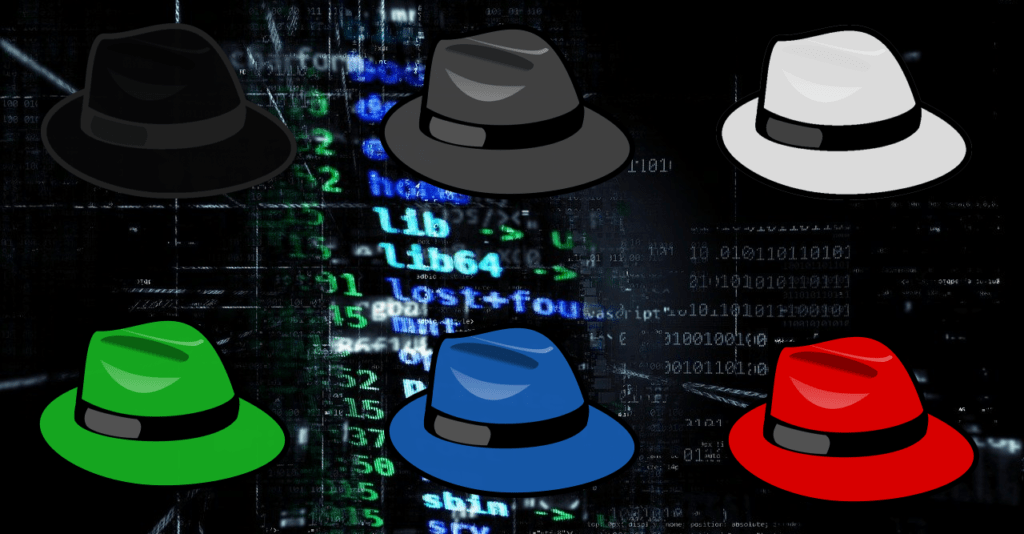
A previous blog article posted in August explained how a group of young hackers compromised over a hundred Twitter accounts. However, not all young hackers exploit systems for criminal purposes. Some use their talents to help companies protect themselves against cyberattacks and data breaches. Earlier this month, Dan Goodin of Ars Technica reported about a hacker team led by a 20-year-old who discovered 55 vulnerabilities within Apple’s corporate network. The 20-yeard-old researcher, Sam Curry, rated 11 of the 55 vulnerabilities as critical because they could have been used to steal private information and take over Apple’s infrastructure. Apple fixed the vulnerabilities and rewarded the team with at least $288,000 in payments. Although hackers often seek financial gain, not all do so maliciously. In general, there are three main types of hackers: white hats, black hats, and gray hats. White hats are ethical, black hats are malicious, and gray hats are somewhere in between. In addition to these three main types, there are various other types of hackers.
Sam Curry’s team are white hat hackers. White hats do not hack systems to commit theft or cause damage. White hats are typically employed by companies to test the security of their systems, and they only try to find vulnerabilities in a system if it is legal for them to do so. Like white hats, gray hats have a code of ethics and typically do not hack systems to commit theft or cause damage. However, unlike white hats, gray hats do not obtain legal permission before trying to hack into a computer or network. If they find a vulnerability, they may offer to disclose it in exchange for a financial reward. Sometimes, if they do not receive compensation, they may decide to share the vulnerability with other hackers. Gray hats may occasionally act as “black hats.” A black hat fits the common and derogatory definition of “hacker” used in the media: an individual who breaks into computer systems for criminal purposes. However, the term “hacker” did not always have a negative connotation. In a security guide written by Red Hat, Inc. and posted on the website of MIT, it is noted that the term “hacker” originally referred to clever members of MIT’s Tech Model Railroad Club in the 1960’s. The term grew to refer to people who were willing “to explore in detail how computer systems and networks function with little or no outside motivation,” and in some circles, “hacker” is a term of respect. In the 1980’s, the term “crackers” was created to refer to black hats. However, this term is not commonly used in modern cybersecurity lingo.
Modern cybersecurity terminology has a few synonyms for “black hat” other than “cracker.” These synonyms include “cybercriminal,” “bad actor,” and just “attacker.” However, they are not completely interchangeable. All black hats are cybercriminals, but not all cybercriminals are black hats. A cybercriminal is someone who uses computers or the internet to commit crimes. Cybercriminals do not always hack into computers and networks. They may instead use the internet for scams, extortion, predation, or other crimes that do not require significant technological expertise. In addition to the synonyms for black hats, there are synonyms for white hats. White hats are also referred to as “ethical hackers,” and it is possible to become a Certified Ethical Hacker (CEH). In addition to white hats and black hats, there are other “hats” that have varying definitions.
The three lesser known hacker types are green hats, blue hats, and red hats. Green hats are novices who lack expertise but are willing to learn more and improve their skills. Green hats are not to be confused with script kiddies, whoonly use pre-existing code and are uninterested in becoming true hackers. According to Sharon Shea of TechTarget, there are two definitions of “blue hat.” White hats employed by Microsoft are called “blue hats.” Outside of Microsoft, blue hats are hackers motivated by vengeance, and are only willing to learn about the tools and techniques they need to get their revenge. Sharon Shea notes that there are different definitions of “red hat” as well. Red hats are either hackers who target Linux systems or hackers who act as vigilantes against black hats. Alpine Security notes that while white hats are focused on defending systems from black hats, vigilante red hats fight fire with fire. They are willing to use viruses, Denial-of-Service (DoS) attacks, and other black hat tactics to destroy a black hat’s cyber infrastructure. Alpine Security considers hacktivists to be a variation of black hats. Like red hats, hacktivists act like black hats for causes higher than financial gain. Unlike red hats, they hack non-black hat targets—including corporations and governments—for political reasons. The hacker group known as Anonymous is an example of a hacktivist group.
Hackers are united by a love of bypassing security systems, but divided into three main types: white hats, black hats, and gray hats. White hats and black hats are polar opposites. Gray hats are not ethical, but not always malicious. “Hacker” is a term of respect in technologically savvy circles, but in the media, “hacker” is often used instead of befitting terms like “cybercriminal.” It is important to understand the context in which the term “hacker” is used, as well as the community using it.