Steganography is the art of hiding secret information in plain sight. Whereas cryptography works by essentially scrambling secret information so that it appears as gibberish until it is unscrambled, steganography works by hiding secret information within a non-secret medium, such as pictures. Steganography is not to be confused with steganalysis, the study of finding information concealed through steganography.
Steganography has been practiced since ancient times. According to Alexey Shulmin and Evgeniya Krylova of Securelist, one early example of steganography is the use of slaves as secret messengers by the Roman Empire. Secret messages would be tattooed on the clean-shaven scalps of slaves. The slaves would be dispatched after their hair grew back, and when they reached the recipients, their heads would be shaved again so that the secret messages could be read. Lily Newman of Wired notes that even Leonardo Da Vinci practiced steganography when he hid messages within his paintings. Steganalysis has also been practiced in the past. In “On the Limits of Steganography” by Ross Anderson and Fabien Petitcolas, the authors discuss how Queen Mary of Scots’ plan to assassinate Queen Elizabeth of England was foiled in 1586 thanks to steganalysis.
Steganography and steganalysis are still practiced, but have evolved in the digital age. In 2017, Kaspersky Lab discovered that cybercriminals were using steganography at an increasing rate. Much like how Da Vinci hid meanings within paintings, cybercriminals can hide data within images and other types of files in order to conduct cyberattacks and espionage. They can embed malicious code within images to create malware hidden from normal anti-virus scans. They can also exfiltrate private information by embedding it within an image and having it sent to them.
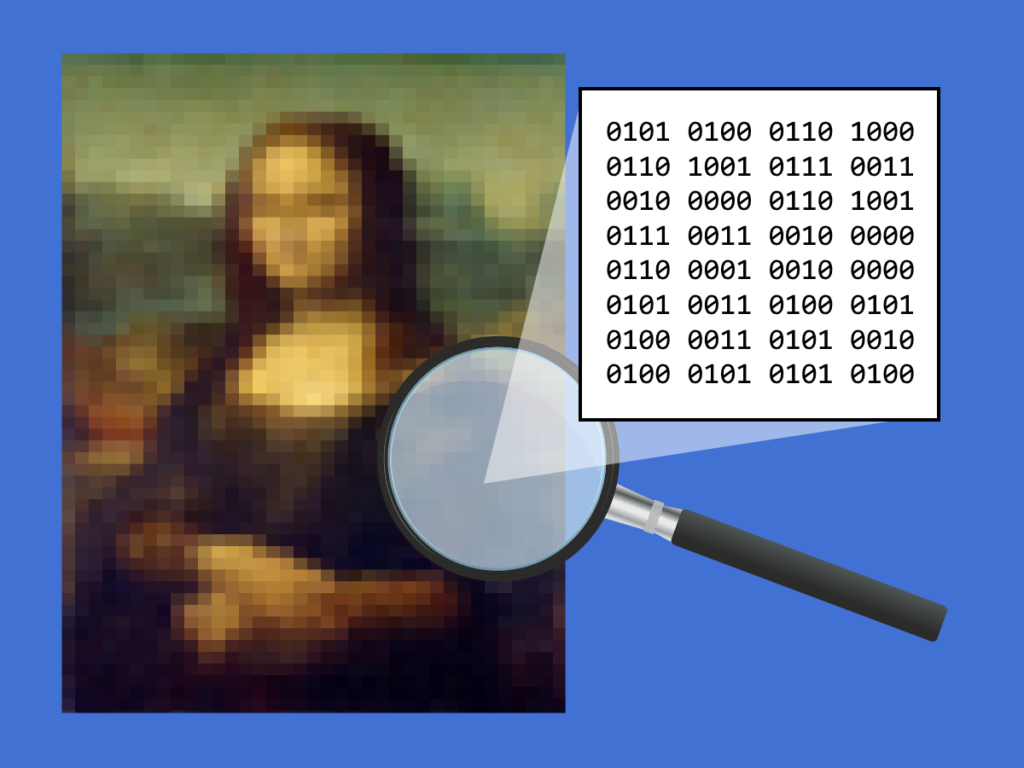
You may wonder how it is possible for malicious code to be hidden within an image. One technique is the use of Least Significant Bit (LSB) steganography. Since digital images are made up of pixels, and both pixel information and malicious code are made up of bits, the bits that form malicious code can be mixed in with the bits that form the image. According to Soumyendu Das, Subhendu Das, Bijoy Bandyopadhya, and Sugata Sanya in their paper “Steganography and Steganalysis: Different Approaches,” steganography for images can be accomplished by modifying the least significant bits (LSBs) of each pixel. Because our ability to perceive color is limited, we cannot perceive the smallest differences in color by one bit. The least significant bits of multiple pixels are combined to form malicious code, but to the viewer, the image looks completely normal.
Images aren’t the only things that bad actors can hide information in. Das et. al. list videos, audio files, plain text files, and even Internet Protocol (IP) datagrams as other potential mediums. The same technique that applies to images can also apply to audio and video files. Das et. al. note that the human auditory system can’t recognize one-bit adjustments to digitized audio, just like how the human eye can’t notice one-bit differences in color. For videos, secret information can be embedded into each frame. For IP datagrams, the bits within the identification and flag fields can be used to carry secret information. However, not all forms of steganography involve binary adjustments. Plain text steganography can involve either mapping the number of extra spaces to a lookup table or selecting specific letters in words based on a provided key. Last year, Igor Kuksov of Kaspersky noted that even Twitter was used by spyware as a medium for steganography.
Not all uses of steganography are harmful. Kuksov noted that Genius.com used steganography to protect their online lyrics from being copied. Although the criminal uses of steganography are difficult to detect, Kuksov provided a few tips to mitigate the threat of malware hidden within media files: carefully reviewing emails that contain media attachments, using official sources to download media, and using anti-virus software to identify suspicious activity that is indirectly related to malicious media. In short, the best ways to protect yourself from this type of malware is to have the same habits that protect you from other forms of malware.