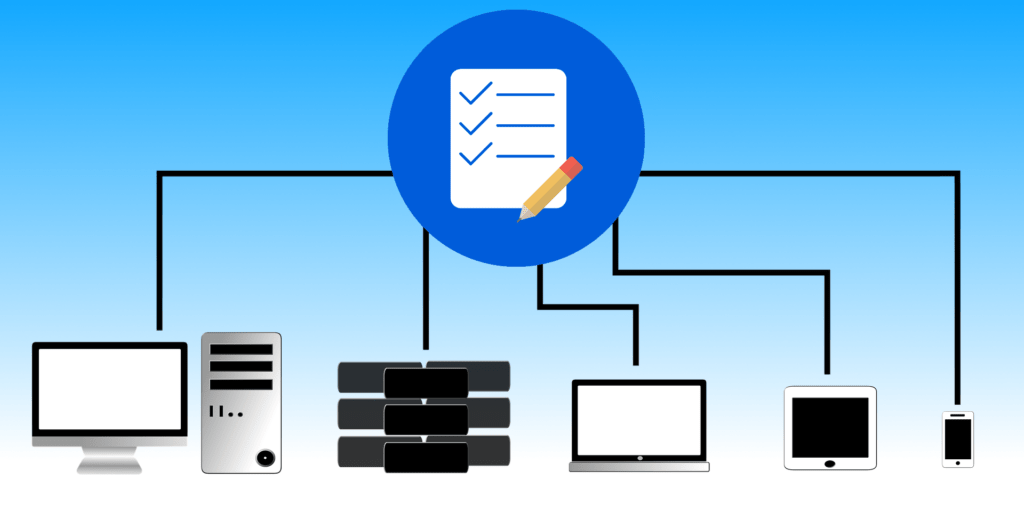
Most organizations rely on IT assets for their day-to-day business operations. IT assets can include the hardware, software, and data used for work. However, organizations may need to inspect their IT infrastructures to make strategic decisions or ensure compliance with federal laws. However, keeping track of every IT asset used for work—including the devices brought in by employees—would be difficult without maintaining a record of all IT assets. This is where Information Technology Asset Management (ITAM) would be useful. According to the International Association of Information Technology Asset Managers (IAITAM), ITAM “is a set of business practices that incorporates IT assets across the business units within the organization. It joins the financial, inventory, contractual and risk management responsibilities to manage the overall life cycle of these assets including tactical and strategic decision making.” Keeping a record of all of an organization’s IT assets is an important practice of ITAM. However, ITAM is about more than just making inventories of IT assets; it is about helping organizations make strategic decisions based on the IT assets they own. There are financial, legal, and security-related applications for ITAM.
Since ITAM is concerned with the life cycles of IT assets, it is applicable to accounting, a field that involves measuring the life cycles of all types of assets. An accountant would want to identify how much money is used to maintain IT assets, how valuable they are, whether or not they have outlived their usefulness, and if money is being wasted. For example, Software as a Service (SaaS) is often paid for with a monthly or annual subscription. If an organization no longer uses a SaaS product for business operations, but is still charged for the subscription, they would be losing money. However, if the organization kept track of its IT assets, they could identify subscriptions that need to be canceled. ITAM would also work well with IT modernization, the practice of upgrading the old parts of an IT infrastructure. By keeping track of IT assets, an organization could identify the old, depreciated assets that need to be replaced to improve performance. Replacing or upgrading IT assets is vital for cybersecurity as well. Outdated IT assets that contain vulnerabilities could be exploited by cybercriminals and disrupt business operations. If IT assets were inventoried, assets with vulnerabilities could be identified and upgraded or replaced so as to nullify potential threats.
In addition to benefitting an organization’s business operations, ITAM could assist with legal matters. David Shepardson and Mike Stone of Reuters reported about regulations that recently took effect and ban U.S. government contractors from using IT assets made by certain manufacturers. The rule was introduced to address concerns related to information security. A complete inventory of a company’s IT assets could be used to identify banned products, and thus help the company achieve compliance. Aside from the new regulations, there are older laws that require companies to verify the security of their IT systems to safeguard customer data. Three examples include: the Health Insurance Portability and Accountability Act (HIPAA), which applies to patient health information; the Gramm-Leach-Bliley Act (GLBA), which applies to consumer financial information; and the Sarbanes-Oxley Act (SOX), which applies to corporate financial information. If one of these laws applies to an organization, they would be liable if their customer data is stolen. Upgrading or replacing vulnerable IT assets would be vital for protecting customer data, and by extension, ensuring compliance with federal laws.
Managing an organization’s IT assets with spreadsheets alone would be a daunting task, which is why there are software tools for ITAM. Some tools specialize in managing software, so they are called Software Asset Management (SAM) tools. Tracking software license subscriptions would be an application of SAM tools. Other tools are used for hardware as well and can scan a network to find connected devices. Sarah White of CIO.com lists some of the popular ITAM solutions. Companies have various reasons to adopt ITAM, and there are various software solutions to choose from. Overall, ITAM and cybersecurity go hand-in-hand. They both improve the performance of an IT infrastructure and help organizations save money in the long run.